The use of digital technology in armed conflict is rising sharply. Such developments come with risks, but they may also provide opportunities. For example, could new technologies help digitally signal that certain infrastructure and assets enjoy protection under international humanitarian law? For 150 years, the red cross and red crescent, and more recently the red crystal, have performed this function in the physical world. Would it be feasible, and advisable from a cyber-security point of view, to mark the digital assets of protected entities in times of armed conflict?
In this post, Tilman Rodenhäuser, Legal Adviser at the ICRC, Laurent Gisel, Head of the Arms and Conduct of Hostilities Unit at the ICRC; Larry Maybee, Legal Adviser at Australian Red Cross; Hollie Johnston, Senior Adviser at Australian Red Cross; and Fabrice Lauper, Technology Adviser at the ICRC present the main concepts and ideas of the ICRC’s research project on the digitalization of the red cross, red crescent, and red crystal emblems.
It is the third year of an armed conflict between the countries of Boronia and Banksia. As the sun rises, two Boronian F-15 fighter aircrafts fly over a city on their way to their pre-planned military objective. What the pilots don’t know, however, is that operational planners have identified the wrong target. Instead of the military warehouse they thought they were targeting, the fighter aircraft pilots are heading to a hospital in Banksia, an establishment servicing a community of 55,000 people.
The pilots reach their objective, readying themselves to drop their guided munitions according to the pre-planned target list. Just before they do so, one pilot notices on the head-up display in her cockpit that the assigned target has something painted on its roof: a large red cross on a white background, about ten square metres. She knows that under international humanitarian law (IHL), medical establishments are protected from attack, and that the red cross is a sign of that protection. She immediately aborts the attack.
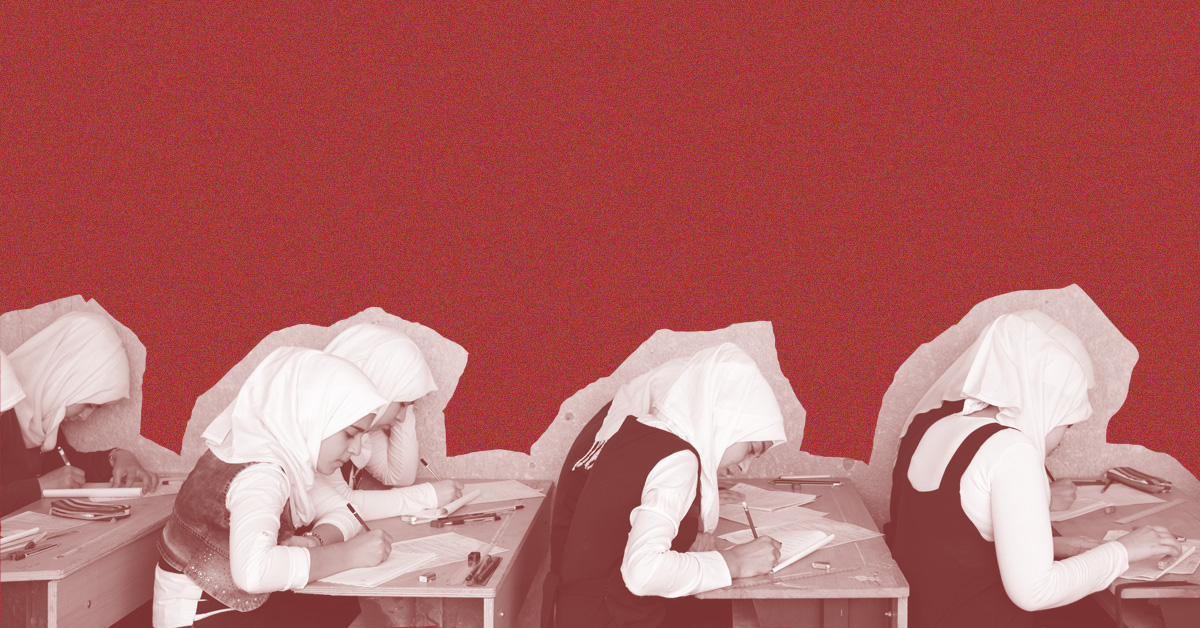
This fictional scenario demonstrates the importance of the distinctive red cross, red crescent and red crystal emblems in identifying personnel, units, establishments, and transports specifically protected under IHL.
Today, warfare is changing. Cyber operations have become a reality of armed conflict, and States are increasingly developing military cyber capabilities. Such developments come with risks, but they may also provide opportunities. For example, could new technologies help digitally signal that certain infrastructure and assets enjoy protection under IHL? What if the Boronians had aimed to deploy malware to disrupt a range of servers they thought were used for military purposes? Could there be a digital emblem, marker or signal indicating whether some of these servers enjoyed the protection for which the distinctive emblems stand?
The ICRC is studying this question with several partners in a research project on the digitalization of the red cross, red crescent, and red crystal emblems. The project examines whether and how the distinctive emblems could be used in the information and communication technology (ICT) environment, taking a critical look at the technical feasibility and protective value of marking the digital assets of protected entities in times of armed conflict.
In this post, we will present the main concepts and ideas that define this project. In two forthcoming pieces, the ETH Zurich Centre for Cyber Trust and Johns Hopkin University Applied Physics Laboratory will present various technical options from their research for marking the digital infrastructure and data of protected entities.
The distinctive emblems: identification and protection during armed conflict
The legal protection of medical facilities during armed conflict is embodied in IHL. The concept at the very core of the First Geneva Convention in 1864, which remains a central notion of IHL to this day, is that the wounded and sick, and those who treat them – medical personnel, their establishments, units, and transports – must be respected and protected in all circumstances during armed conflict (see, for instance, Rules 25, 28, and 29 of the ICRC’s Customary IHL Study).[1]
For 150 years, the red cross and red crescent, and more recently the red crystal, have given visibility to these protections, showing that those who wear them, or facilities and objects marked with them, are protected against harm (see Rule 30 of the ICRC’s Customary IHL Study). The core instruments of IHL (see Article 44 of the First Geneva Convention and Article 18 of Additional Protocol I) authorize and regulate the use of the emblems by the medical and religious services of the armed forces, as well as authorized civilian medical units and transports during armed conflict. The emblems also identify and protect the ICRC and the International Federation in times of armed conflict, and other members of the International Red Cross and Red Crescent Movement (the Movement) when carrying out medical activities in wartime.[2]
Traditionally, IHL conceives of the emblems in a physical form – a large red cross, red crescent or red crystal on a white background. When affixed or displayed on protected persons or objects, the emblem serves as the visual expression of the legal protection accorded to them.
The obligation to respect and protect such persons and objects is not, however, limited to kinetic warfare; it also extends to cyber operations conducted in the context of an armed conflict. And the need for signaling this protection to cyber operators is significant: cyber operations against medical facilities are happening and risk causing harm to humans, in particular in times of armed conflict when the preservation of functional medical systems and infrastructure is urgently needed. Similarly, as the ICRC – and other components of the Movement – are increasingly digitalizing their systems and operations, there is a real risk that they too will fall victim to hostile cyber operations.
The question of a ‘digital emblem’
In the search for concrete measures to strengthen the protection of medical services of armed forces and other authorized medical and humanitarian entities during armed conflict, the idea of developing a new signal, digital marking, or other means of identification in cyberspace (i.e. a ‘digital emblem’) has emerged as a possible solution. A key advantage of such a concept is that it could become part of the internationally recognized legal and policy framework for the ‘distinctive emblems’ or ‘distinctive signals’ (such as light, radio and electronic signals, see Annex 1 of Additional Protocol I).
Over recent years, the ICRC has raised the idea of a ‘digital emblem’ in discussions with cyber security and operational experts, who identified benefits but also certain risks (see here (pp. 9; 39-42) and here (pp. 27-31). On the one hand, a ‘digital emblem’ could mark the infrastructure and data of protected actors to facilitate their identification and help avoid erroneous targeting, or incidental effects caused by, cyber operations. On the other hand, a digital signal risks identifying a set of ‘soft targets’ to malicious actors, which could be more easily and systematically targeted. Moreover, malicious actors could misuse a ‘digital emblem’ to falsely identify their operations as having protective status under IHL. These benefits and risks are not new, however, and also exist also in the physical world; the question is, whether and how they are different in the ICT environment.
A research and consultation process to assess the feasibility and protective value of a ‘digital emblem’
In 2020, the ICRC initiated a project to examine technical means to identify digital infrastructure and data belonging to entities entitled to use the distinctive emblems.
The ICRC initially partnered with two research institutions: the ETH Zurich Centre for Cyber Trust and Johns Hopkin University Applied Physics Laboratory to identify technological means of marking the digital infrastructure and data of protected entities. The ICRC has now partnered with Australian Red Cross (ARC) to consult with a geographically diverse group of cyber experts to examine the solutions proposed by the researchers and discuss the potential risks, benefits, and challenges associated with the development of a distinctive emblem or signal in cyberspace. This consultation is forthcoming and will include cyber security and operational experts from a range of different backgrounds.
The objective of these consultations is to assess whether a ‘digital emblem’ may be expected to enhance the protection against harmful cyber operations for those entitled to use it. If this assessment identifies a viable and protective solution, this will not mark the end of the examination of whether and how the distinctive emblems could be used in the ICT environment, but rather the beginning of a new process, or stage, of the ‘digital emblem’ project.
From a technical standpoint, prototypes of a ‘digital emblem’ would need to be developed and tested. And importantly, the ICRC – following its mandate to ‘work for the understanding and dissemination of knowledge of international humanitarian law applicable in armed conflicts and to prepare any development thereof’ – would need to present possible solutions to States and discuss ways to include them in the existing legal framework. Further discussions would also need to occur with other relevant stakeholders, notably the wider Red Cross and Red Crescent Movement.
* * *
Regardless of the outcome, the project constitutes an important reflection of how the existing IHL framework can address and accommodate developments in technology. Potentially, the results of this research project could impact the way belligerents operate in cyberspace. Think back to the example presented at the start of this post . . .
It is now the fourth year of the armed conflict.
Banksia has started developing a malware that spreads automatically and affects a cloud-based software used by Boronia to manage its military supply logistics. While doing reconnaissance, the Banksian cyber command realized that the targeted software is more commonly used than previously expected, including on systems that are marked by a newly developed ‘digital emblem’. Upon further investigation, the operators realize that these systems belong to a hospital.
The Banksian cyber command knows that distinctive emblems and signals are a sign of protection. The commander directs the team to reprogram their malware to ensure that it does not affect digital infrastructure belonging to the hospital. Alerted to the use of the software by medical units thanks to the digital emblem and effective reconnaissance, the commander directs programmers to review procedures and program cyber capabilities in a way that their harmful effects cannot be triggered by systems marked by a digital emblem.
[1] They lose their protection if they are being used, outside their humanitarian function, to commit acts harmful to the enemy.
[2] At all times, components of the Movement may use the emblem to identify their units, transports, personnel and volunteers. This is defined as ‘indicative use’. When used as an indicative device, the emblem must always be displayed together with the name or the initials of the Movement component concerned and in small dimensions.
See also
- Antonio De Simone, Brian Haberman, Erin Hahn, Identifying protected missions in the digital domain, September 23, 2021
- Felix E. Linker & David Basin, Signaling legal protection during cyber warfare: an authenticated digital emblem, September 21, 2021
- Kubo Mačák & Ewan Lawson, Avoiding civilian harm during military cyber operations: six key takeaways, June 15, 2021
- Kubo Mačák, Tilman Rodenhäuser & Laurent Gisel, Cyber attacks against hospitals and the COVID-19 pandemic: How strong are international law protections? April 2, 2020
- Helen Durham, Cyber operations during armed conflict: 7 essential law and policy questions, March 26, 2020
- Laurent Gisel and Tilman Rodenhauser, Cyber operations and international humanitarian law: five key points, November 28, 2019









Legal protection is a need to everyone but sensitisation is need and advocacy in the community.
I want to learn more about the legal