***
Cyber attacks and infections regularly affect governments, militaries and private companies in many sectors around the world. Every year, they cost governments and private businesses billions in loss of income, recovery costs and required investments in cyber security. Some estimations show that the actual or potential damage caused by a single cyber attack can reach billions of dollars. However, it is important to underscore that the effects of cyber operations may go beyond monetary loss. While fortunately there have not been reports of a cyber attack having caused death to date, the past years have seen an evolution towards attacks disrupting the delivery of essential services to the population and attacks designed to cause physical effects.
The ICRC’s interest in cyber space stems from the great importance of cyber space for the ICRC as a humanitarian organisation. We notably rely on cyber space for our communications, including when bringing protection and assistance to victims of armed conflicts and, more generally, when working in remote field areas. Our interest also stems from our concerns about the potential human cost of cyber operations, in particular during armed conflict. Assessing the potential humanitarian consequences of new technologies that may be used in conflict is indeed part of the ICRC’s long-standing mandate. While most cyber attacks are not linked to an armed conflict, various types of cyber operations have been used during armed conflicts. Appraising the effects of cyber operations in general may also help understand their potential human cost during conflicts.
What effects can cyber operations cause? Three examples from 2017
WannaCry was a piece of malware (malicious software) that spread in May 2017, using an exploit called EternalBlue for automatic propagation among Windows operating systems. It disrupted the operations at many companies and public services providers in 150 countries. Notably, 80 health clinics in the U.K. were affected, leading to the cancellation of 19,000 appointments, including 139 urgent referrals.
About a month later, NotPetya used the same EternalBlue exploit, but included additional spreading components. NotPetya was an automatic and self-propagating wiper designed to impair system functionality. It appears that it impacted systems first in Ukraine and then spread to systems in other countries. Affecting manufacturing plants and logistical conglomerates in addition to other sectors, it impacted transportation and logistics, leading to congestion at 76 ports around the world. The estimated costs were substantial, over a billion dollars.
Finally, Triton, a custom-designed malware with the capability to disrupt industrial safety systems was discovered in 2017. Safety instrumented systems (SIS) ensure that the industrial processes operate in a controlled manner, within safety margins. Tampering with this critical safety layer may lead to physical destruction and possibly—subject to specific circumstances—even injury or death. Some reports indicate that these effects may have even been among the goals of the attack.
The potential human cost of cyber operations
While cyber attacks with physical effects are rare, the landscape is evolving. Despite the fact that the reach and consequences of most cyber attacks have, to date, been limited, some operations have demonstrated the capacity to cause serious effects—or were designed to do so—as is illustrated by the three examples just discussed. Furthermore, actors are continuously adapting their techniques and the capabilities differ significantly among the different threat actors. The question of the human cost of cyber operations will thus be of importance in the years to come.
The healthcare sector
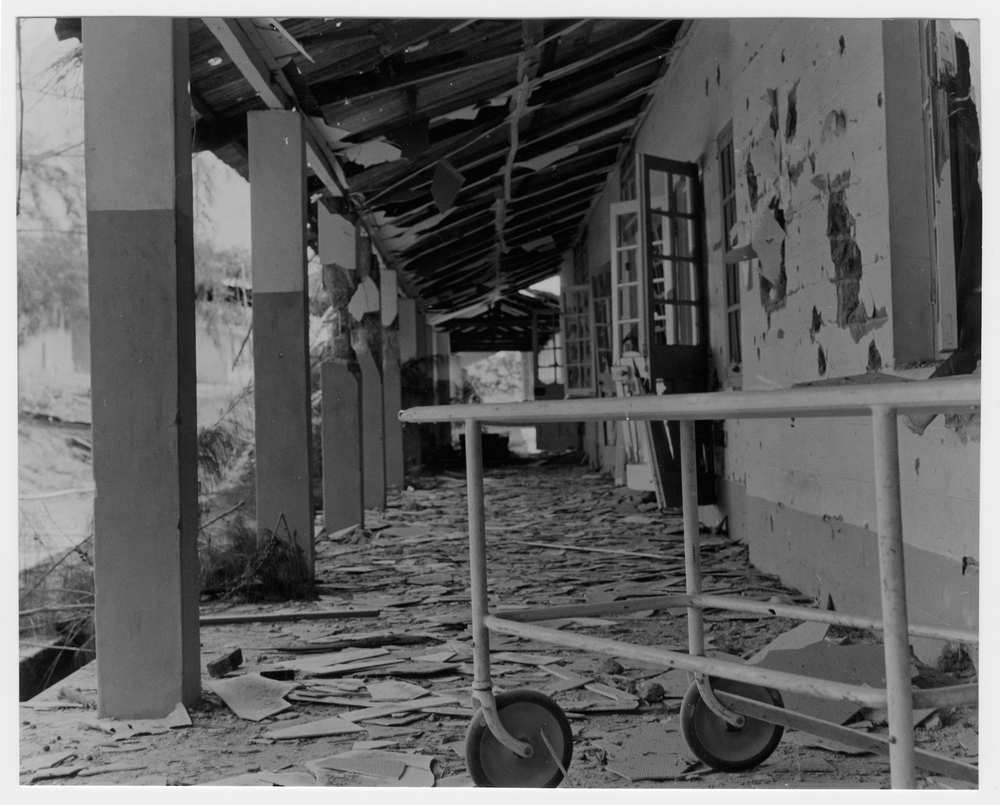
Of special importance is cybersecurity and risk in the healthcare sector, as is the ability of hospitals and other services to continue providing healthcare to civilian populations when affected by cyber attacks. Cyber attacks on—and infections in—the healthcare sector are on the rise. Ransomware infections that impact the availability of medical data or systems, and that affect the provision of health services are a growing challenge. WannaCry underlined the complex question of the security posture of the health sector. While the consequences of a coordinated attack that would affect all health care providers in one area and thus prevent referral to a fully functioning facility remain unclear, they are concerning. In parallel, a dangerous trend is emerging where actors seem to be targeting healthcare sector suppliers. Attacks tampering with medical devices could potentially lead to the administration of wrong doses, impact the technical processes of diagnosis or affect the proper functioning of life-supporting instruments such as pacemakers. In extreme cases, this could potentially result in life-threatening risks.
Cyber attacks against industrial systems
Cyber attacks targeting industrial systems are developing rapidly, both in terms of technical capabilities and an increase in the number of threat actors involved. They may affect other sectors providing essential services for the population—such as, for example, electricity and water—and in specific cases potentially result in physical damage.
The energy sector was estimated this year to be the one most commonly attacked (38.7%) among industries affected by cyber attacks on facilities with industrial control systems (ICS). While not many detailed examples are available to the public, the threat landscape is evolving and attacks are becoming more sophisticated. For example, the 2016 cyber attacks that affected the Ukrainian electricity grid demonstrated an increase in automation compared to those of 2015. There are also several cases of cyber attacks affecting power plants, including nuclear power plants. Persistent cyber operations’ campaigns show how attackers try to gain access to operational systems, which potentially could be used later for more disruptive purposes.
Water treatment facilities are also increasingly dependent on ICS, which potentially renders them vulnerable to cyber attacks. For example, in 2015 attackers were able to manipulate valves to cause a change of the chemical mix at a water treatment facility. Fortunately, in this case the change was detected and the negative effects minimized. Recently, ransomware infections occurred at the outset of a natural disaster (a hurricane). This highlights how cyber attacks that take place in difficult situations can complicate recovery.
Past track record of publicly known cyberattacks against industrial facilities demonstrates their feasibility and ability to cause physical damage, as evidenced by cases such as Stuxnet, the ‘inability of a proper shut down of a furnace [at a German steel mill] resulting in unexpected conditions and physical damage to the system’, and the disruption caused by the Triton malware already mentioned. Attacks on critical networks and the ability to interfere with industrial equipment may require specialised resources, like the access to expertise and equipment. Cyber operations targeting industrial sites could potentially be very dangerous and carry with them real risk of humanitarian consequences.
Cyber attacks having systemic effects
Lastly, one cannot look at the human cost of cyber operations without discussing attacks against the core internet services and other attacks having systemic effects, in view of many systems’ reliance on the internet. While the inbuilt redundancy of the internet makes it highly resilient, it is important to understand the risks faced by certain critical components such as the DNS root servers or trust systems. Furthermore, as technology evolves, paradigm shifts like the Internet of Things (and DDoS botnets formed out of IoT devices) or the increasing role of cloud computing providers (which if affected with a down time, could have regional and global consequences) introduce new challenges. Many other critical systems are also important, in particular the global financial system (i.e., SWIFT network).
To better assess the potential human cost of cyber operations, it is important to understand the evolving nature of the threats, including the constraints, and resources needed to design and execute a disruptive or destructive attack. The security posture and resilience of systems—in particular those providing essential services to the populations—is also key to understanding the potential consequences of cyber attacks.
Cyber operations during armed conflicts and their limits
Some of the operations discussed above affected countries involved in armed conflicts. However, it is often hard to conclude in a definitive manner whether a cyber operation has any nexus to an armed conflict. This is because typically no one claims responsibility for the cyber operations and attribution of such operations is a challenging and often lengthy process. Although this situation complicates the analysis for external observers, no such difficulty exists for those responsible for the operation.
As noted by the UN Group of Governmental Experts (GGE), ‘it is in the interest of all States to promote the use of ICTs for peaceful purposes and to prevent conflict arising from their use’. While some States expressed opposition to the militarization of—or an arms race in—cyber space, it is estimated that between 20 and 30 States either have, or are building, offensive capabilities in cyber space. The United Kingdom and the United States have confirmed their use of cyber operations in the conflict against the Islamic State group.
Of course, any resort to force by a State—whether physical or through cyber space—remains constrained by the United Nations Charter. Even if no international humanitarian law (IHL) treaty expressly mentions cyber weapons, there is no question for the ICRC that IHL applies to and restricts the use of cyber capabilities as means and methods of warfare during armed conflicts, as it does for any other new technology used in conflict. It is important, however, to underscore that the application of IHL neither justifies a use of force that would violate the UN Charter nor encourages the militarization of cyber space. The point of the application of IHL is that—in addition to, and independent of, the requirements of the UN Charter—any State choosing to develop or use cyber military capabilities—be they for defensive or offensive purposes—must ensure that they do not violate IHL.
The protection afforded by IHL against the effects of cyber operations during armed conflicts
Even during armed conflicts, the choice of means and methods of warfare is not unlimited. Of particular relevance for cyber operations is the prohibition of weapons which are indiscriminate by nature. The use of other weapons is also not unrestricted. Notably, any use must respect the principles of distinction, proportionality and precautions. In particular, attacks must not be directed at civilians or civilian objects. Critical civilian infrastructure—including the cyber infrastructure on which they operate or rely—are civilian objects and therefore protected against attack, unless they have become military objectives.
This begs the question of which cyber operations amount to an attack for the rules governing the conduct of hostilities under IHL. Even during armed conflict, not every incident of hacking, intrusion or infection would be an attack as defined under IHL. While few, if any, would dispute that a cyber operation designed to kill or cause physical damage would qualify as such an attack, various views have been expressed on whether a cyber operation designed to interfere with the functionality of a computer system or network is an attack. In the view of the ICRC, an overly restrictive understanding of the notion of attack would be difficult to reconcile with the object and purpose of the rules on the conduct of hostilities, which is to ensure the protection of the civilian population and civilian objects (2015 IHL Challenges Report, p 41). This debate has obvious and crucial consequences for the protection that IHL affords.
Additionally, some categories of objects enjoy specific protection. For example, hospitals must be respected and protected, which renders cyber attacks against the availability or integrity of medical data unlawful (2015 IHL Challenges Report, p 43). Moreover, it is prohibited to attack, destroy, remove or render useless objects indispensable to the survival of the civilian population, such as drinking water installation. This includes the ICT infrastructure required for their functioning.
While a growing number of States, international organisations and armed forces have asserted that IHL applies to, and therefore restrict the use of, cyber operations during armed conflicts, so far few States have expressed views on how IHL applies. Applying pre-existing IHL rules to such new means and methods of warfare, however, raises the question of whether the rules are sufficiently clear in light of the specific characteristics of cyber operations and their foreseeable human cost. Furthermore, States that develop cyber military capabilities must ensure that such capabilities can be used in accordance with international law, which also requires clarity with regard to how the law applies. In his regard, the commitment of the Commonwealth Heads of Government to ‘move forward discussions on how … applicable international humanitarian law, applies in cyberspace in all its aspects’ is welcome.
International efforts towards a more secure cyber space
While the topic of cyber security has been on the agenda of the international community since 1999 when the UN General Assembly adopted a resolution submitted by the Russian Federation, several recent initiatives have given the efforts renewed impetus in the past few days. Last Thursday, the Global Commission on the Stability of Cyber Space proposed six new norms. The following day, the First Committee of the United Nations General Assembly adopted two draft resolutions. One foresees the creation of an open-ended working group and the other foresees a request to the Secretary General to establish a new Group of Governmental Experts. And Monday, 51 States, as well as a few hundred private companies, academia and other organisations, endorsed the Paris Call for Trust and Security in Cyber Space.
In light of this background, we are excited today to kick off a 2.5-day meeting of experts on the potential human cost of cyber operations. During the meeting—with the help of cybersecurity experts from around the world, as well as participants with policy, legal and military expertise—we will consider the issues discussed above.
We will reflect on the past, current and foreseeable evolution of cyber capabilities in order to gain a better understanding of the possible consequences. Our focus will be on the risks of death, injury and physical damage, as well as disruption to the provision of essential services to the civilian population. Taking a unique view on cyber threat intelligence from a humanitarian perspective, issues we will look at include: the capabilities of the cyber space threat actors; malware building and the risk of tools reengineering; the execution of hostile cyber operations and how can such operations be targeted and controlled; the resources needed; and, the cyber security posture and resilience of the systems considered.
The discussions will aim to build a better understanding of the offensive and defensive aspects of cyber operations, as well as the avenues in the technical, policy, legal or other realms to reduce or avoid the potential human cost of cyber operations. Although cyber operations are nothing new and they may have been used in different forms for about two decades now, it is difficult not to acknowledge the accelerated pace of their evolution in the last years.
We will publish a report of the meeting next year. Watch out for its announcement on the ICRCs’ law and policy blog.
***
Laurent Gisel, Senior Legal Adviser and Lukasz Olejnick, Scientific Adviser on Cyber, Legal Division, International Committee of the Red Cross.






Dear Laurent and Lukasz, Thank you for this very interesting and important article. You can count on my support for your work.
Best wishes,
Véro
I appreciate your efforts you take to dig deep into matters and find their relationship with humanterian law. thank you and i just argue to continue and soon I will do the same