The significance of technology and internet access for modern society cannot be understated. Current estimates assess there are between four and five billion global internet users connecting on one or more devices every day. Over the past few decades, this technology has fundamentally changed how we communicate, learn, conduct business, manage critical infrastructure, and execute government affairs.
The internet has also played an undeniably crucial role in enabling remote workforces worldwide in the wake of the COVID-19 pandemic. However, while the benefits are numerous, the interconnected nature of this medium, and its freedom to cross international borders, has led many governments to establish military elements for the dual purpose of defending their national interests, as well as projecting power. In the last decade alone, military cyber units have evolved at a substantial rate, while cyber attacks attributed to advanced persistent threats have now become commonplace headlines in our daily news cycles.
These developments, in a domain where international law is recognized to apply, but where specific international norms are still fairly nascent, accentuate the need for governments to thoroughly consider the risks of civilian harm that may result as byproducts of their cyber operations. This blog explores future developments in military cyber operations along the themes of Artificial Intelligence, the Internet of Things, and recent State-sponsored cyber events.
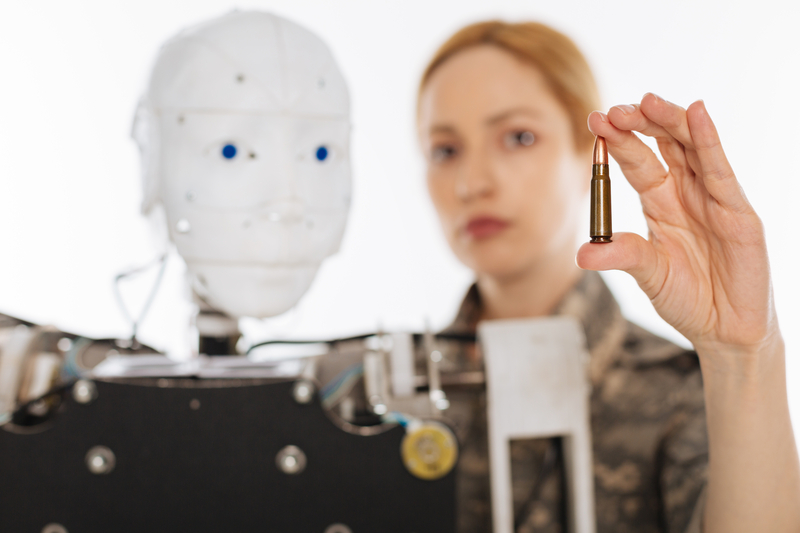
Artificial Intelligence
The application of machine learning has accelerated at a rapid pace as governments and technology companies seek to capitalize on efficiencies of scale and automation in the cyber domain. In 2016, while responding to a challenge proposed by the US Department of Defense, a company named ForAllSecure introduced a system called Mayhem. This system demonstrated it was possible for a computer to find, test, and patch vulnerabilities in real time. Less than five years later, every major cybersecurity vendor now stresses the crucial role that machine learning plays in allowing their products to identify anomalies and issue timely protections at scale. Further, they stress that this technology is now a necessary element of any defensive cyber solution due to the increased sophistication and automation of adversary campaigns.
However, it should be noted that machine learning and automation are just a subset of the technological advancements needed to develop fully autonomous Artificial Intelligence (AI) systems. Over 50 nations have published national strategies driving their respective priorities in the field, which recognize the numerous, emerging applications and potential benefits that AI can provide to society. Several prominent technology companies have also joined the effort. IBM’s Watson Health solution serves as a prime example, as it assists healthcare providers with medical diagnosis, tracking viral incidence, and more. Conversely, we have also seen what happens when AI technology performs in an unexpected manner. For example, in 2016 Microsoft introduced an AI-powered chatbot on Twitter that, within hours, began posting inappropriate messages.
While the worldly impacts of a chatbot are relatively minor, governments recognize that unreliable technology in military applications often results in far more significant consequences. As such, while military cyber operations will likely continue to leverage machine learning and automation to achieve their objectives, it is unlikely they will make the leap to fully autonomous AI systems for offensive operations in the near future. Responsible governments understand that cyber operations have the potential to cause global impacts, and for that reason alone they will continue to require human operators capable of making informed risk decisions regarding civilian harm when conducting any form of offensive cyber operations (see also the ICRC’s new report at p. 33).
Internet of Things (IoT)
The number of devices that are being connected to the internet is significant. In the late 1990s and early 2000s, self-propagating computer worms were significant threats that often infected internet-connected computers on a massive scale. The key to their success was twofold, in that computers lacked security protections and they were connected directly to the internet where they were able to communicate freely.
To combat these threats, in 2004, Microsoft released Windows XP Service Pack 2, which for the first time enabled firewall protections by default. This provided a layer of security for the computers running the system. In more recent years, we have also welcomed the introduction of home routers. By design and function, home routers provide an added benefit in that they typically serve as a gateway separating our home devices from the raw internet and in many cases contain additional security features to restrict undesired network traffic.
Considering the lessons of the past, the present proliferation of IoT devices demonstrates a concerning trend. While these IoT devices allow us to have ‘smart’ internet-connected doorbells, thermostats, refrigerators, televisions, and security cameras, to name just a few, the reality is that very few of these devices come with any sort of security software to detect or defend against cyber threats. A research study of 1.2 million IoT devices published in 2020 found that 98% of devices relied on unencrypted network traffic, 83% of medical imaging devices were running on unsupported software, and 57% of all devices were vulnerable to medium or high severity attacks. However, it is noteworthy that this study was published four years after the Mirai botnet gained access to hundreds of thousands of IoT devices worldwide, used them to launch cyber attacks, and demonstrated just how vulnerable IoT devices really were. It therefore remains concerning that, given the benefit of time and experience, we have witnessed minimal progress towards advancing the security of these devices.
As it applies to military cyber operations, the native vulnerabilities associated with IoT devices typically increase the attack surface for organizations worldwide. However, while the risk of civilian harm can often be managed by targeting specific IoT devices, the opposite is true for cyber operations that target vulnerable devices indiscriminately. Therefore, it becomes imperative that nations evaluate the significant risks associated with conducting cyber operations involving IoT devices as it is often difficult to discern the impact they may have on medical facilities, critical infrastructure, educational institutions, and other sensitive networks.
Recent cyber events
Without a doubt, the COVID-19 pandemic has forced us all to adapt and change how we interact with technology. Through a cybersecurity lens, we watched as organizations accelerated their adoption of cloud technologies and shifted towards VPN solutions in order to extend access to corporate networks for remote employees. In doing so, this shift dramatically changed the size and shape of networks as the workforce moved from easily identifiable office buildings to a remote, geographically dispersed workforce.
Consistent with this change, we also observed a troubling shift in the conduct of cyber operations. Two noteworthy cyber events of the past year include the SolarWinds supply chain compromises, and the more recent Microsoft Exchange Server compromises in March 2021. While both events were conducted outside the scope of an armed conflict, they highlight an emerging trend where cyber operations are being conducted below the threshold of armed conflict, and therefore outside of the scope of the protections that international humanitarian law (IHL) affords to civilians. As noted on page 34 of the ICRC’s new report, this results in the activities becoming ‘difficult to classify from a legal perspective’ and contribute to a ‘lack of clarity regarding the applicable legal framework and to the blurring of military and civilian roles in cyberspace’.
For the SolarWinds event, it is assessed that a nation-State cyber actor pursued an approach to compromise a company that makes enterprise-level network monitoring software. Once inside, the actor then injected malicious code into a routine update that was downloaded by an estimated 19,000 customers.
Conversely, for the recent Microsoft Exchange attacks, a nation-State cyber actor discovered several 0-day vulnerabilities that could be exploited to gain privileged access to Microsoft email servers worldwide. This capability was initially used for targeted collection; however, when Microsoft issued a security patch to address the vulnerability, the actor responded by compromising tens of thousands of organizations worldwide.
Comparing the two events, there is an obvious connection between networks that have become more dispersed due to remote employment, and at least two reported state-sponsored Advanced Persistent Threats (APTs) that have demonstrated a willingness to shift towards indiscriminate cyber operations. While espionage may have been these actors’ original intent, given the benefit of time, it has become clear that both of these operations have resulted in harm to thousands of civilian institutions, including local businesses, schools, medical facilities, and critical infrastructure owners who are forced to take systems offline and remediate malicious code across their networks.
In light of these two recent cyber events, concerns regarding vulnerable IoT devices, and advancements in Artificial Intelligence, it is clear that common understandings need to be reached by States on how international law protects civilian populations against cyber operations. The ICRC’s report on Avoiding Civilian Harm from Military Cyber Operations during Armed Conflicts is a tremendous step forward in acknowledging the complexities of this topic and should serve as a catalyst for the further development and interpretation of norms and legal rules that prevent harm to civilians during military cyber operations.
See also
- Ellie Shami, Assessing the risks of civilian harm from military cyber operations during armed conflicts, June 22, 2021
- Noëlle van der Waag-Cowling, Stepping into the breach: military responses to global cyber insecurity, June 17, 2021
- Kubo Mačák & Ewan Lawson, Avoiding civilian harm during military cyber operations: six key takeaways, June 15, 2021
- Tilman Rodenhäuser, Kubo Mačák, Even ‘cyber wars’ have limits. But what if they didn’t?, March 9, 2021




Comments